2 weeks
Lost investigating cosmetic edits that unexpectedly changed sales funnel behavior.
Argus makes sure you never lose revenue from a broken flow — find out the moment something breaks, not days later.
We pull live data on the call. You leave with a clear picture of what's broken and what it's costing you — even if you don't hire us
Silent regressions don't always throw errors — they just quietly break revenue flows while your dashboard looks healthy
2 weeks
Lost investigating cosmetic edits that unexpectedly changed sales funnel behavior.
$44,600
Lost after a website change quietly broke Meta Pixel tracking and ad optimization.
$6,000
Burned in one weekend after an API key was deployed publicly and abused for AI token usage.
Regression monitoring at every push — your team ships, we make sure all business-critical flows work as intended
1,000+
Flows currently protected
Covering critical integrations (e.g. Stripe, Meta Ads, Supabase) and critical customer interactions (e.g. checkout, auth, conversion funnel).
$780K
Dollars currently monitored
Total monthly revenue value passing through monitored flows across active customer setups.
200+
Incidents prevented
We catch silent regressions and risky changes before they happen in production.
Argus is built to monitor the business flows that actually drive your revenue
| Price | Accuracy | Speed | Scalability | |
|---|---|---|---|---|
| ArgusBuilt to catch silent business-flow regressions before they hit users | ||||
| In-house software engineerLacking the context to catch every potential edge case and revenue leak | ||||
| CodeRabbitBuilt for code correctness, not business correctness, with no understanding of revenue impact | ||||
| ClaudeGreat for shipping code, but missing production awareness and proactive monitoring of external dependencies | ||||
| FreelancersTask-based support with inconsistent continuity, increasing the surface area for potential risk |
We plug into the tools founders already use to ship fast
Built for founders who want real accountability, fast support, and zero lock-in
01
Talk directly to Victor and our lead engineer in Slack from day one.
No ticket queue, no handoffs, no "we'll get back to you next week."
02
Stay because it works, not because you're trapped in a contract.
If we're not protecting your revenue, you can walk anytime.
03
Our scanners run continuously across your critical flows, including nights and weekends.
Regressions don't wait for office hours, and neither do we.
04
If we can't identify at least 5x our fee in revenue risk, you shouldn't pay us.
Simple, measurable, and aligned with outcomes.
05
You get clear weekly updates on what ran, what failed, what we fixed, and what it cost.
When something breaks, we respond in under 30 minutes.
06
We map your critical flows manually with you - checkout, attribution, onboarding, and more.
Nothing important gets missed by auto-detection guesswork.
If we can't show real revenue risk fast, don't hire us.
Our cancellation flow stopped working and we didn't catch it in time. With Argus in place, I ship on my own with way more peace of mind. We've cut about 30 hours a month in software engineer costs.
We're still early in traction at around $1K MRR, and with just me and my cofounder it gets stressful fast. Victor, Rahul, and Maxime are super fun and helpful. I don't feel bad for my mistakes anymore - they've seen everything it seems. With Argus on Slack, I'm so much happier.
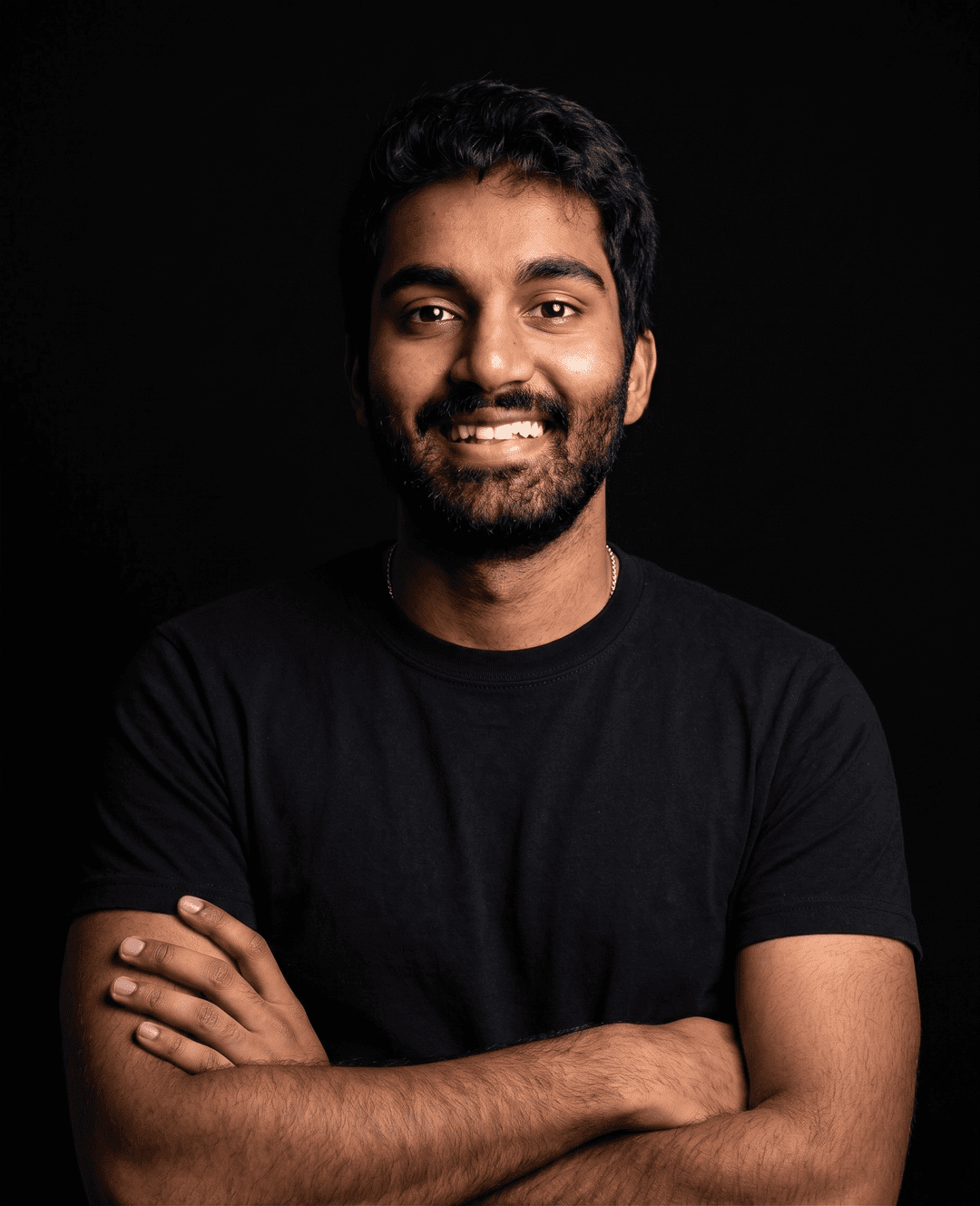
Rahul
FOUNDER | CEO
I know how painful it is when building to release changes that hurts your business in invisible ways.
I built an e-commerce brand, got it to $10K MRR, and had to deal with every kind of break along the way:
That's why I built Argus - so founders don't have to fight this alone. Let me show you what's breaking your revenue before it costs you more.